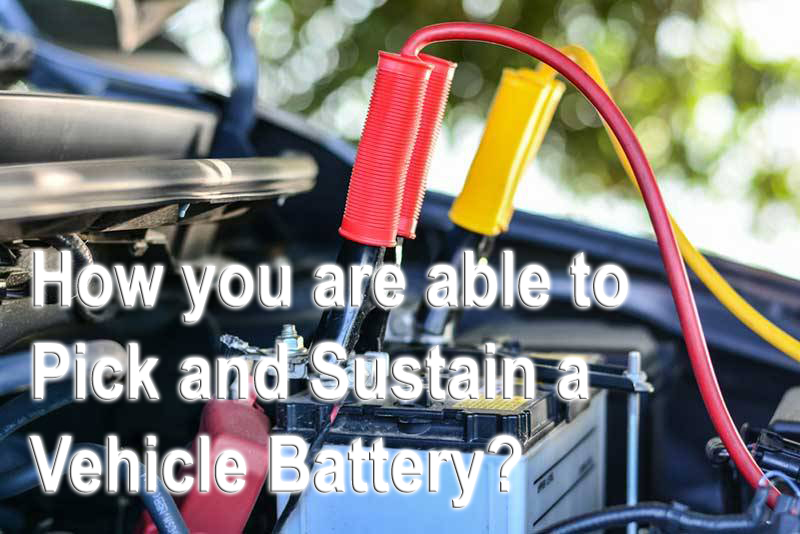
Do I Want a Car Battery Jump Starter or perhaps a Super Capacitor?
The car battery jump starter of nowadays is a wonderful appliance. Additionally to possessing the power to begin a car having a dead battery, lots of those devices have additional characteristics. These extra characteristics can modify a jump starter into a true survival tool.
A Number Of The Further Characteristics Found On Car Battery Jump Starters Are:
- A light attachment. You might use the jump starter inside the dark. In the event the light source is LED, then the power consumption is low. When you have other further functions, you may be working with the jump starter for something besides getting a car started.
- An inverter or AC power source. The energy inside a jump starter is DC (Direct Current) power. Our property appliances are AC (Alternating Present). European AC is 50 cycle and North America is 60 cycle. These are not compatible. Verify the owner’s manual for the kind